SHA1:
- 87e690b5aa60dbb549d8d7e118dc06e4d4314732
A dropper Trojan written in an incorporated programming language of “1C:Enterprise”. The Trojan is designed to run a ransomware Trojan on the infected computer—Trojan.Encoder.567—that is stored in its resources as a payload.
The dropper is distributed via email attachments to the message which is titled
Subject: Our BIC code has been changed
and has the following text:
Greetings! Our BIC code has been changed. Please update your bank classifier. The classifier can be updated automatically in 1C Enterprise 8. File – Open classifier update processor from the attachment. Click YES to update the classifier automatically. Within 1-2 minutes if there is Internet connection.
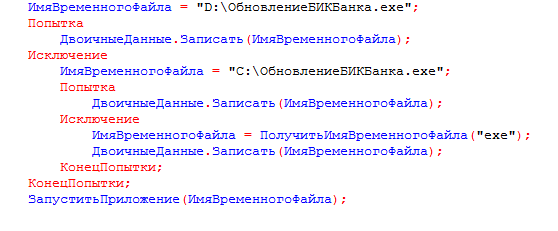
The message contain an EPF file ПроверкаАктуальностиКлассификатораБанков.epf that is implemented as an external data processor for the 1C:Enterprise platform. Its body is protected with a password and looks as follows:
If the user run the attached file in 1C: Enterprise mode, the following window is displayed:
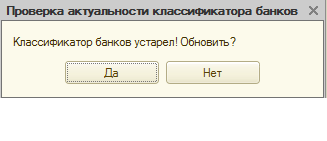
Clicking on any button of this window will launch 1C.Drop.1. First, it searches the 1C database for contractors with known email addresses and then sends the text message with its own copy attached. The message is determined by the following code:
Текст = Письмо.Тексты.Добавить(“Greetings! Our BIC code has been changed.
|Please update your bank classifier.
|The classifier can be updated automatically in 1C Enterprise 8.
|File – Open classifier update processor from the attachment.
|Click YES to update the classifier automatically.
|Within 1-2 minutes if there is Internet connection.
Письмо.Вложения.Добавить(ИмяФайла, "ОбновитьБИКБанка.epf");The Trojan uses the email address specified in the victim’s 1C user account as the sender’s address. If the user has not specified their email, the Trojan substitutes it with 1cport@mail.ru and attaches the ОбновитьБИКБанка.epf external data processor that contains the Trojan’s copy.
If the file is run in the 1C software, the ransomware Trojan will affect the computer as well; yet, this copy of 1C.Drop.1 will send contractors a corrupted EPF file that cannot be opened with “1C:Enterprise”.
1C.Drop.1 supports the following 1C databases:
- Trade Management 11.1
- Trade Management (basic) 11.1
- Trade Management 11.2
- Trade Management (basic) 11.2
- Accounting 3.0
- Accounting (basic) 3.0
- 1C:Comprehensive Automation 2.0
Finally, the Trojan extracts Trojan.Encoder.567 from its resources and runs it on the infected computer.