SHA1:
- 83b15e545f96239ef43ff5f94c582e1a3e8361f3
A detect for the component of Android.Loki.16.origin which infects Android devices. Android.Loki.16.origin downloads and unpacks this module together with several exploits. Then it tries to get root privileges. If successful, Android.Loki.28 is run with elevated privileges.
Once launched, Android.Loki.28 checks some arguments and mounts the section /system for a writing process. Then this module loads one of the randomly selected libraries— libz.so, libcutils.so or liblog.so—to the memory.
Then Android.Loki.28 retrieves two malicious components from its body:
- xalco (Android.Loki.26);
- lib{NAME}.so (Android.Loki.27), where NAME is a randomly generated string containing the same number of characters as a name of the selected library.
These component are then saved to the system catalogs /system/bin/ and /system/lib/ respectively.
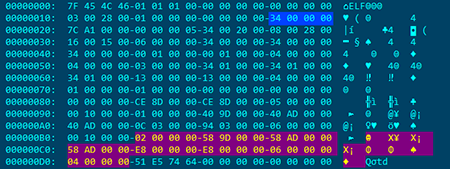
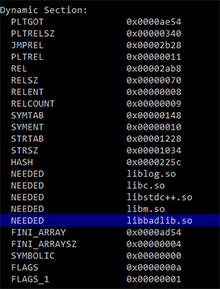
Android.Loki.28 then injects a dependency from the module Android.Loki.27 into the selected library. For this, the module finds a segment table of the library in the memory and searches for the segment PT_DYNAMIC (information about dynamic linking). An example below shows the highlighted necessary segment:
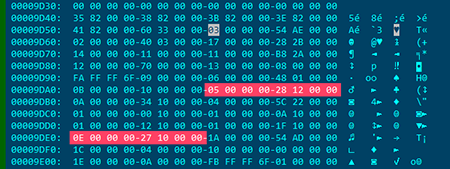
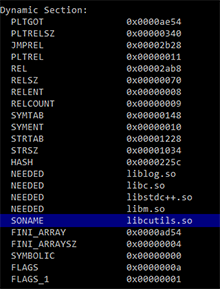
Once the necessary segment is found, Android.Loki.28 searches values of the tags DT_STRTAB (table address with strings) and DT_SONAME (an offset in relation to DT_STRTAB used to write the name of the attacked library):
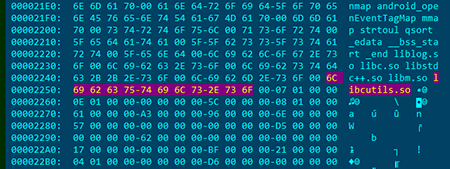
Once the module finds a necessary string with a name of a targeted library, this name is then modified to the name of the unpacked module Android.Loki.27. Then Android.Loki.28 replaces the tag DT_SONAME to DT_NEEDED. Thus, instead of the name of a system library, one more dependency from the module Android.Loki.27 is stored on its place.
Such modification does not hinder the library’s operation and allows Android.Loki.27 to be run together with the library every time it is called by the system.
However, if Android.Loki.27 is removed, Android will not be booted correctly, and a device will go out of order. To restore the system, the device’s firmware should be updated by using an original system image.